Disclaimer: This article is for educational and informational purposes only. It does not constitute professional cybersecurity advice. Always consult a qualified security professional before making changes to your organization’s security infrastructure.
Why Pros Are Quietly Ditching Antivirus for Better Security
If you still think antivirus software is the backbone of your cybersecurity strategy, you might be surprised to learn that some of the sharpest security minds in the industry have already quietly moved on.
They are not abandoning protection. They are upgrading it, and the tools they are choosing instead are fundamentally changing how organizations defend themselves in 2025 and beyond.
Introduction: The Antivirus Era Is Ending and Cybersecurity Professionals Know It
Picture this: a hospital network gets hit by ransomware. The antivirus software was fully updated. The firewall was running. Every box was checked. And yet, attackers slipped through undetected for eleven days before anyone noticed.
This is not a hypothetical. Scenarios like this play out hundreds of times a year across industries, and they reveal a painful truth: the tools we built our defenses around in the 1990s were designed for a world that no longer exists.
Antivirus software was brilliant for its time. It worked by scanning files for known malicious signatures, essentially checking a list of known bad actors at the door. But today’s attackers do not show up on any list. They morph, evolve, live off the land using your own system tools against you, and operate in memory where traditional antivirus never even looks.
Cybersecurity professionals are not abandoning antivirus out of recklessness. They are doing it because they understand something the wider public has not quite caught up to yet: signature-based detection is like bringing a 1990s map to navigate a city that rebuilt itself overnight. It is not that the map is wrong. It is that the streets have completely changed.
This post breaks down the surprising alternatives that security teams are now quietly prioritizing, why these tools outperform traditional antivirus in today’s threat landscape, and what this shift means for anyone trying to build a genuinely modern security posture. Whether you work in IT, run a business, or just care about protecting your data, this is the conversation worth having right now.
How Antivirus Software Became a Cybersecurity Blind Spot
Antivirus software was never designed to handle what modern attackers throw at it. It was built around a simple idea: collect signatures of known malware, scan incoming files, block matches. Clean and logical.
The problem is that cybercriminals long ago figured out how to beat this system. They now routinely use techniques like polymorphism (where malware rewrites its own code), fileless attacks (where nothing is ever written to disk), and living-off-the-land binaries (where attackers use legitimate Windows or Linux tools to do the dirty work). None of these approaches trigger traditional antivirus detection, because there is no malicious file to scan.
Think of it this way. Traditional antivirus is a bouncer checking ID against a list of banned names. Fileless malware does not have a name on the list, because it never formally existed as a file at all. It just shows up, does damage, and leaves.
Cybersecurity professionals working at major enterprises have been raising this alarm for years. According to research tracked by security analysts, the majority of successful breaches today involve tactics that antivirus software is architecturally incapable of catching. That is not a bug in the antivirus product. That is a fundamental limitation of the approach.
This is why the shift away from antivirus is not a trend or a fad. It is a rational response to a changed threat environment, driven by professionals who have seen too many incidents play out with antivirus blinking green right up until the moment everything fell apart.
Endpoint Detection and Response: The Antivirus Alternative Cybersecurity Professionals Trust Most
If there is one technology that has done more to replace antivirus than anything else, it is Endpoint Detection and Response, or EDR.
EDR tools do not just scan for known threats. They continuously monitor every endpoint (laptops, servers, workstations, mobile devices) for suspicious behavior, recording rich telemetry data and using behavioral analytics to spot patterns that suggest an attack is underway, even if that attack uses no known malware at all.
Imagine a security camera system versus a bouncer checking IDs. Antivirus is the bouncer. EDR is the camera system that records everything, flags unusual behavior, and lets investigators rewind and reconstruct exactly how a breach unfolded. That forensic capability alone is worth its weight in gold when something goes wrong.
Why cybersecurity professionals prefer EDR:
- Detects threats based on behavior, not just known signatures
- Provides full attack chain visibility so teams can understand what happened and contain it
- Enables real-time response actions like isolating an infected endpoint remotely
- Generates detailed forensic timelines that help prevent repeat incidents
- Integrates with threat intelligence feeds to stay current with emerging attack patterns
Leading EDR platforms include CrowdStrike Falcon, SentinelOne, Microsoft Defender for Endpoint, and Carbon Black. These tools have become near-standard in enterprise security stacks, and their adoption is accelerating rapidly in mid-market companies as prices and complexity have dropped significantly in recent years.
EDR is not perfect. It requires skilled analysts to interpret alerts, and alert fatigue is a real challenge in high-volume environments. But for cybersecurity professionals serious about catching modern threats, EDR is now the baseline, not the ceiling.
Extended Detection and Response: When Antivirus Alternatives Go Enterprise-Wide
EDR focuses on endpoints. XDR, or Extended Detection and Response, takes that same behavioral monitoring philosophy and stretches it across your entire infrastructure: cloud workloads, email, network traffic, identity systems, and more.
Where antivirus looks at individual files and EDR looks at individual endpoints, XDR stitches together signals from every corner of your environment and looks for the bigger story. A suspicious login from an unusual location that is followed by abnormal file access and then an outbound connection to a known bad IP address: none of those three events alone screams “breach,” but together they tell a very clear story. XDR surfaces that story automatically.
This cross-domain correlation is enormously powerful, because modern attacks are rarely confined to a single system. Attackers move laterally, escalate privileges, and pivot between systems over days or weeks. XDR is designed specifically to catch that kind of slow-burn intrusion that a perimeter firewall and an antivirus scanner would never see.
What XDR brings to the table over traditional antivirus:
- Unified detection across endpoints, cloud, email, and network in a single console
- Automated correlation of signals that would otherwise be siloed and invisible
- Dramatically reduced mean time to detect (MTTD) and mean time to respond (MTTTR)
- Native integration with SIEM (Security Information and Event Management) platforms
- AI-powered threat hunting that flags anomalies without requiring manual rule writing
Vendors like Palo Alto Networks, Microsoft, Trend Micro, and Cisco have all built robust XDR platforms. For larger organizations running complex hybrid environments, XDR is increasingly the architecture of choice, and for good reason.
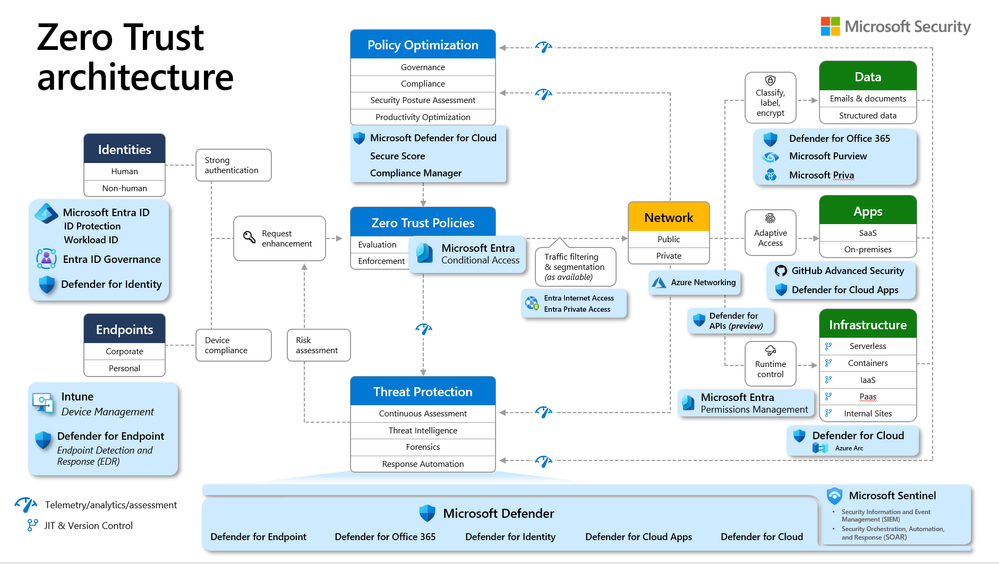
Zero Trust Architecture: The Antivirus Alternative That Changes the Game Entirely
Traditional security, including antivirus, was built on a perimeter model. You built walls, checked who came in at the gate, and assumed that anything already inside was safe. Zero Trust flips this model completely on its head.
Zero Trust operates on one foundational principle: never trust, always verify. No user, device, or system is automatically trusted just because it is inside your network. Every request for access, every connection, every transaction is continuously authenticated and validated against strict policy rules before it is allowed to proceed.
This approach makes antivirus look like a speed bump by comparison. Even if a piece of malware or a compromised account manages to enter your environment, Zero Trust architecture limits what it can do dramatically. Lateral movement, which is the lifeblood of most ransomware attacks, becomes exponentially harder when every hop across your network requires fresh authentication.
The core pillars of Zero Trust security:
- Verify identity continuously, not just at login
- Enforce least-privilege access so users and systems only touch what they need
- Microsegment the network so breaches cannot spread freely
- Monitor all traffic, including internal traffic, for anomalous behavior
- Apply strict device health checks before granting access
Zero Trust is not a product you buy. It is an architecture you build, often by layering tools like identity providers (Okta, Azure AD), privileged access management platforms, and network segmentation tools. That complexity is real, but security teams that have implemented Zero Trust report dramatically reduced blast radius when incidents do occur.
According to McKinsey’s top insights on cybersecurity transformation, organizations implementing Zero Trust architectures consistently report lower breach costs and faster containment times compared to perimeter-reliant security models.
Behavioral Analytics and UEBA: Spotting Threats Antivirus Never Could
User and Entity Behavior Analytics, commonly called UEBA, takes a fundamentally different approach to threat detection. Instead of looking for malicious files, it builds a behavioral baseline for every user and system in your environment and then alerts when something deviates from that baseline.
Think of it as the security equivalent of your credit card company noticing you suddenly bought a hundred dollars of gas in a city you have never visited. No fraud signature was triggered. The card was not stolen. But the behavior was unusual enough to warrant a flag.
UEBA does exactly this for your network. If a finance analyst who normally accesses payroll files on Tuesday mornings suddenly logs in at 2 a.m. from a new device and starts downloading large volumes of HR records, UEBA catches it. Antivirus would not even blink.
Where UEBA adds the most value:
- Detecting insider threats, both malicious employees and compromised accounts
- Catching credential theft scenarios where attackers use valid login credentials
- Identifying data exfiltration that unfolds gradually over days or weeks
- Surfacing privilege abuse that policy controls missed
- Reducing false positives by understanding what “normal” actually looks like for each entity
Platforms like Splunk, IBM QRadar, and Microsoft Sentinel all incorporate UEBA capabilities. For organizations worried about insider risk or the growing problem of compromised credentials (which now account for the majority of initial breach vectors), UEBA is a tool antivirus simply cannot replace.
Cloud Security Posture Management: Protecting the Infrastructure Antivirus Cannot Touch
Here is something that often catches people off guard: antivirus software has essentially no relevance to your cloud security. It cannot scan your AWS S3 bucket configurations, your Azure IAM policies, or your Kubernetes cluster settings for dangerous misconfigurations that attackers love to exploit.
Cloud Security Posture Management, or CSPM, fills that gap entirely. CSPM tools continuously audit your cloud environment against security best practices and compliance frameworks, flagging misconfigurations before attackers find them and do it for you.
The numbers around cloud misconfiguration are genuinely alarming. The majority of cloud breaches do not happen because attackers defeated cutting-edge security tools. They happen because a storage bucket was left publicly accessible, an overly permissive IAM role was forgotten, or a security group rule was misconfigured during a rushed deployment. CSPM tools exist specifically to catch these kinds of human errors before they become headlines.
What CSPM monitors and manages:
- Storage bucket permissions and public access settings
- Identity and access management policy configurations
- Network security group rules and firewall configurations
- Encryption settings for data at rest and in transit
- Compliance posture against frameworks like SOC 2, ISO 27001, and PCI-DSS
Leading CSPM tools include Wiz, Prisma Cloud from Palo Alto Networks, and AWS Security Hub. As organizations run more workloads in the cloud, CSPM has moved from a nice-to-have to a genuine security essential, covering an entire attack surface that antivirus software simply cannot see.
Deception Technology: The Antivirus Alternative That Turns the Tables on Attackers
Deception technology is one of the most clever approaches in modern cybersecurity, and it works on a principle that antivirus could never contemplate: luring attackers into a trap.
The idea is to seed your environment with honeypots, fake credentials, decoy files, and phantom systems that look real to an attacker but serve no legitimate business purpose. Any interaction with these decoys is an immediate, high-confidence signal that something malicious is happening, because no legitimate user or system would ever touch them.
This approach flips the detection challenge upside down. Instead of trying to identify malicious behavior from millions of legitimate actions, you create a clearly marked minefield and wait for attackers to step on it. The signal-to-noise ratio is extraordinary compared to traditional security tools.
The unique advantages deception technology provides:
- Near-zero false positives, because only attackers interact with decoys
- Early detection of lateral movement, often catching attackers during reconnaissance
- Rich attacker intelligence that reveals tactics, techniques, and procedures
- Works against both external attackers and malicious insiders
- Buys defenders critical time to respond before significant damage is done
Companies like Attivo Networks (now part of SentinelOne), Illusive Networks, and Cymulate offer deception technology platforms. While this approach is more commonly seen in mature enterprise security programs, it is gaining ground rapidly as organizations look for ways to shift from reactive to proactive threat detection.
Threat Intelligence Platforms: Giving Cybersecurity Professionals the Foresight Antivirus Lacks
Antivirus software is inherently reactive. It needs to know about a threat before it can protect you from it. Threat intelligence platforms flip that dynamic by equipping security teams with knowledge about emerging threats, attacker infrastructure, and campaign activity before it hits their environment.
Threat intelligence comes in several flavors. Strategic intelligence helps security leaders understand the broader threat landscape relevant to their industry. Tactical intelligence provides technical indicators like malicious IP addresses, domain names, and file hashes. Operational intelligence tracks specific attacker groups and their current campaign activity.
When used well, threat intelligence turns your security posture from reactive to genuinely predictive. Instead of waiting for an attack to trigger an alert, your team actively hunts for indicators of compromise tied to threat actors known to target your industry, blocking infrastructure before attacks even launch.
How modern cybersecurity professionals use threat intelligence:
- Enriching EDR and SIEM alerts with context about the attacker behind the threat
- Proactive blocking of malicious infrastructure before attacks are launched
- Informing vulnerability prioritization so teams patch what attackers are actually exploiting
- Sharing intelligence with industry peers through Information Sharing and Analysis Centers (ISACs)
- Guiding red team exercises based on real threat actor tactics and techniques
Platforms like Recorded Future, Mandiant (now part of Google), and ThreatConnect provide threat intelligence capabilities that no antivirus tool can approach. According to the World Economic Forum’s best practices in global cybersecurity resilience, organizations that actively integrate threat intelligence into their security operations report meaningfully better detection and response outcomes.
Security Awareness Training: The Human-Centered Antivirus Alternative No One Talks About Enough
Here is an uncomfortable truth: your employees are the most targeted and most effective attack vector in most breaches. Phishing emails, social engineering, vishing calls, fake login pages. These attacks do not need to bypass your antivirus because they target people, not systems.
Security awareness training is not glamorous. It does not have a slick dashboard or a threat detection algorithm. But study after study has shown that organizations with mature, continuous security awareness programs suffer significantly fewer successful phishing attacks and social engineering breaches than those relying primarily on technical controls.
Think of it this way. You can have the most sophisticated EDR platform in the industry, and it will not stop an employee from typing their credentials into a convincing fake login page. But an employee who has been trained to spot suspicious emails, verify unexpected requests through a second channel, and report anomalies immediately: that employee is a security control in their own right.
What effective security awareness training looks like:
- Simulated phishing campaigns that test and train employees in realistic scenarios
- Role-based training tailored to what different departments actually encounter
- Regular micro-learning updates, not just annual compliance checkboxes
- Clear, easy-to-use mechanisms for reporting suspicious activity
- Positive reinforcement culture that rewards vigilance rather than punishing mistakes
Platforms like KnowBe4, Proofpoint Security Awareness Training, and Cofense have built entire businesses around this problem. Combined with technical controls, a well-trained workforce is one of the most cost-effective investments any organization can make in its overall security posture.
Patch Management and Vulnerability Management: The Unglamorous Antivirus Alternative That Stops Most Attacks
If you had to pick one thing that would prevent more breaches than anything else, it would not be a fancy AI-powered detection system. It would be consistently patching known vulnerabilities before attackers exploit them.
The uncomfortable reality is that the majority of successful cyberattacks exploit vulnerabilities that patches were already available for at the time of the breach. Attackers are extraordinarily efficient at scanning for and exploiting known, unpatched weaknesses. They do not need zero-days when organizations consistently take months to patch critical vulnerabilities.
Modern vulnerability management goes well beyond just pushing patches. It involves continuously scanning your environment for weaknesses, prioritizing remediation based on actual exploitability and business criticality, and tracking remediation progress with the same rigor you would apply to any other business process.
A mature vulnerability management program includes:
- Continuous asset discovery so you know everything that exists in your environment
- Regular vulnerability scanning of all assets, including cloud infrastructure
- Risk-based prioritization using threat intelligence to focus on what is actually being exploited
- Automated patching where safe and feasible to reduce remediation timelines
- Clear SLAs for remediation based on vulnerability severity
Tools like Tenable, Qualys, and Rapid7 lead this space. When combined with EDR and Zero Trust architecture, a rigorous patch management program addresses the foundational weaknesses that most breaches rely on, doing far more effective work than any antivirus scanner running in the background.
Antivirus vs. Modern Cybersecurity Alternatives: An Honest Comparison
| Security Approach | What It Detects | Response Capability | Cloud Coverage | Insider Threat Protection | Modern Threat Effectiveness |
|---|---|---|---|---|---|
| Traditional Antivirus | Known malware signatures | Block/quarantine files | None | None | Low |
| EDR | Behavioral anomalies, fileless attacks | Isolate endpoint, kill process | Partial | Moderate | High |
| XDR | Cross-domain attack chains | Coordinated multi-system response | Full | Moderate | Very High |
| Zero Trust Architecture | Anomalous access patterns | Block/re-authenticate | Full | High | Very High |
| UEBA | Behavioral deviations per user/entity | Alert and block | Moderate | Very High | High |
| CSPM | Cloud misconfigurations | Alert and auto-remediate | Full | None | High (cloud-specific) |
| Deception Technology | Lateral movement, credential theft | Alert, gather intelligence | Moderate | High | High |
| Threat Intelligence | Emerging TTPs and attacker infrastructure | Proactive blocking | Full | Moderate | Very High |
| Security Awareness Training | Human-layer social engineering | Behavior change | N/A | High | High |
| Vulnerability Management | Known unpatched weaknesses | Remediation prioritization | Full | None | Very High |
The table above paints a clear picture. Traditional antivirus addresses a narrow slice of the modern threat landscape. Every alternative on this list addresses attack vectors that antivirus cannot touch, often providing proactive rather than purely reactive protection.
This is not about choosing one tool over all others. Most mature security programs stack multiple layers. But the shift in the industry is clear: antivirus has moved from the foundation of a security strategy to, at most, one small layer among many, and many security professionals are dropping it from their stacks entirely in favor of the more capable alternatives listed above.
The Myths Keeping Organizations Stuck on Antivirus Software
Cybersecurity professionals moving away from antivirus often encounter genuine resistance, and a lot of that resistance comes from deeply held myths that deserve a direct response.
Myth 1: Antivirus is required for compliance. Reality: Most modern compliance frameworks like SOC 2 Type II, ISO 27001, and NIST CSF do not mandate antivirus specifically. They require effective endpoint protection, which EDR typically satisfies more completely than antivirus anyway. Many compliance auditors are actively receptive to well-documented antivirus replacement strategies.
Myth 2: Something is better than nothing. Reality: Antivirus that gives a false sense of security is potentially worse than knowing you have gaps. Organizations that believe their antivirus is protecting them from modern threats may under-invest in the controls that would actually help.
Myth 3: Only large enterprises need advanced tools. Reality: Attackers do not discriminate by company size. Small businesses are frequently targeted precisely because they are assumed to have weaker defenses. Many modern EDR and Zero Trust tools have scaled down significantly in cost and complexity for smaller organizations.
Myth 4: Antivirus is good enough if you also have a firewall. Reality: Firewalls and antivirus protect different layers and both were designed for a perimeter model that modern hybrid and cloud environments have largely outgrown. Layering two legacy controls does not produce a modern security posture.
Myth 5: Replacing antivirus is too expensive and disruptive. Reality: The cost of a ransomware incident, data breach, or regulatory penalty typically dwarfs the cost of transitioning to a modern security stack. The disruption of migration is real but manageable with proper planning.
How to Start Transitioning Away from Antivirus Without Creating New Risks
Making this shift thoughtfully matters. Ripping out antivirus without replacing it with something better is not the goal. The goal is to build a security posture genuinely suited to the current threat landscape.
A practical migration approach for cybersecurity professionals:
- Assess your current stack honestly. What threats are you actually worried about? What gaps exist in your current detection and response capabilities? Start with an honest inventory.
- Start with EDR as your endpoint foundation. Most organizations transitioning away from antivirus begin by deploying EDR alongside their existing antivirus, validating the EDR’s coverage, and then removing antivirus once they are confident the new tool is performing as expected.
- Layer Zero Trust principles progressively. You do not have to implement Zero Trust overnight. Start with identity (strong MFA, conditional access policies) and expand from there.
- Add threat intelligence context. Even basic threat intelligence feeds integrated into your existing SIEM dramatically improve the quality of your alerts and accelerate response.
- Invest in your people. Security awareness training is cheap relative to the value it provides. Run simulated phishing campaigns quarterly and make security reporting easy and psychologically safe.
- Close cloud visibility gaps. If you run any workloads in the cloud, CSPM should be a priority. Misconfigurations are one of the most exploited attack surfaces in modern breaches.
- Measure what you can defend. Track metrics like mean time to detect, mean time to respond, and patch SLA compliance. Visibility into these numbers is essential for continuous improvement.
This migration is not a weekend project. For most organizations, it takes months and requires genuine organizational commitment. But the security professionals who have made this shift consistently report higher confidence in their defenses and better outcomes when incidents do occur.
What This Shift Means for the Future of Cybersecurity Careers
The move away from antivirus is not just a technology story. It is also a skills story, and it has real implications for anyone building or advancing a cybersecurity career.
Employers are not posting job listings that say “experienced in antivirus management.” They are looking for people who understand behavioral detection, threat intelligence, cloud security architecture, Zero Trust design, and incident response using modern EDR and XDR platforms. The skills premium has shifted dramatically toward these modern disciplines.
Cybersecurity roles commanding premium salaries in 2025:
- Threat Hunter: Uses EDR and threat intelligence platforms to proactively seek out attackers. Average salary range: $110,000 to $160,000.
- Cloud Security Engineer: Designs and manages CSPM, cloud IAM, and cloud-native security tools. Average salary range: $130,000 to $190,000.
- Identity and Access Management Specialist: Implements Zero Trust identity frameworks. Average salary range: $115,000 to $165,000.
- Security Operations Center (SOC) Analyst (Tier 2/3): Operates EDR and XDR platforms, performs incident response. Average salary range: $95,000 to $145,000.
- Detection Engineer: Builds detection logic for SIEM and EDR platforms. Average salary range: $120,000 to $175,000.
The common thread across all of these roles is that they require skills built around the modern security tools replacing antivirus. Professionals who proactively develop these competencies are positioning themselves for the most in-demand and highest-compensated roles in the industry.
Conclusion: The Quiet Revolution Is Already Underway
The cybersecurity professionals quietly moving away from antivirus are not being reckless. They are being clear-eyed about the limitations of a tool that was genuinely excellent for its era but was not built for this one.
Modern attackers operate with sophistication, patience, and creativity that signature-based detection cannot touch. Fileless malware, credential theft, cloud misconfigurations, insider threats, and supply chain attacks are not fringe scenarios. They are the dominant patterns in the breach landscape right now.
The tools replacing antivirus, including EDR, XDR, Zero Trust, UEBA, CSPM, deception technology, threat intelligence, and security awareness training, address this reality with approaches that are behavioral, contextual, continuous, and proactive. They represent a fundamentally different philosophy of security, one built for a world where attackers are already inside your perimeter and the question is how quickly you can find them and contain them.
This shift is not about abandoning caution. It is about channeling it more effectively, toward tools and practices that are actually built for the threats organizations face today.
If you are a security professional already navigating this transition, you are ahead of the curve. If you are just beginning to question whether your antivirus is doing the job you think it is, that question is the right one, and the alternatives are more accessible and affordable than they have ever been.
The future of cybersecurity is behavioral, intelligent, and cloud-native. The organizations and professionals who embrace that reality early will be the ones best positioned to protect what matters most.
What to Do Next
Share this post with your IT team or a colleague still running antivirus as their primary defense. The conversation it starts might be one of the most valuable ones you have this year.
Read Next:
- Zero Trust Architecture: A Plain-English Guide for Security Leaders
- EDR vs. XDR: Which Platform Actually Fits Your Organization?
- The Cybersecurity Skills Gap in 2025: What Employers Are Actually Hiring For
Drop a comment below: Has your organization already made the shift away from traditional antivirus? What tools did you move to, and what surprised you most about the transition? Your experience could help someone else make a better decision.
This content was produced for educational purposes. Always consult a qualified cybersecurity professional before modifying your organization’s security architecture or tooling.