Apple Intelligence Features: Secret iPhone AI Tools You Need Now
Apple Intelligence Features: Secret iPhone AI Tools You Need Now Your iPhone just became the smartest device you own, and you’re probably using less than half of what it can…
Read more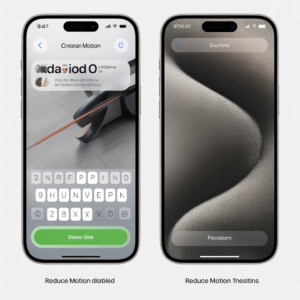
Make Your Old iPhone Feel Brand New Again (Hidden Hack)
How to Make Your Old iPhone Feel Brand New Again: The Hidden Performance Hack Apple Doesn’t Advertise Your iPhone used to be fast. Snappy. Almost magical. Now it lags, stutters,…
Read more
Shocking Dark Web Tools Hackers Use to Steal Identities
The Secret Dark Web Tools Hackers Use to Steal Identities — And How to Check If You’re Already a Victim Your personal data may be sitting in a hacker’s shopping…
Read more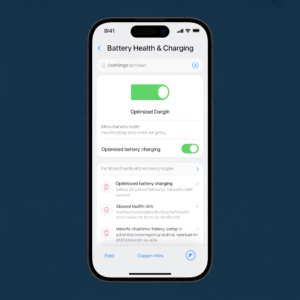
Warning: This iPhone Charging Habit Is Killing Your Battery
Warning: This Common iPhone Charging Habit Is Secretly Destroying Your Battery You plug your iPhone in every night before bed. You wake up, it’s at 100%, and life is good….
Read more
Shocking: How AI Steals Your Identity in 60 Seconds
How Cybercriminals Are Using AI to Steal Your Identity in Under 60 Seconds You did everything right. Strong password. Two-factor authentication. You never click suspicious links. And yet, a cybercriminal…
Read more
Unbelievable: Automate Your Business Free with AI Tools
Unbelievable: How I Secretly Automated My Entire Business in 30 Days Using Free AI Tools Thirty days ago, I was drowning. Emails piling up, social posts unscheduled, invoices late, customer…
Read more
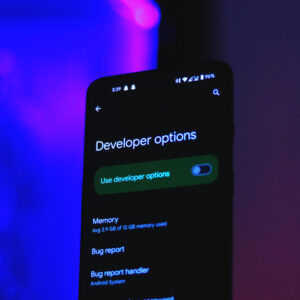
Turn Your Old Android Into a Pro Security Camera (Free)
Unbelievable: How to Turn Any Old Android Phone into a Professional Security Camera That old Android phone sitting in your drawer right now? It is already a professional security camera….
Read more
Clone iPhone Without iCloud — The Method That Actually Works
Revealed: Can You Really Clone Your iPhone to a New Device Without iCloud? The Unbelievable Method Completely Explained Introduction Over 1.5 billion active iPhones are in use worldwide right now…
Read more
Phishing Attacks That Bypass Two-Factor Authentication Explained
Revealed: The Terrifying New Phishing Attack That Bypasses Two-Factor Authentication Completely Introduction Over 80% of hacking-related breaches still involve stolen or compromised credentials — and now, the one defence you…
Read more