The Secret Dark Web Tools Hackers Use to Steal Identities — And How to Check If You’re Already a Victim
Your personal data may be sitting in a hacker’s shopping cart right now, priced at less than a cup of coffee.
That sounds dramatic. It isn’t. Right now, on hidden marketplaces buried inside the dark web, cybercriminals are buying and selling full identity packages — your name, Social Security number, address, date of birth, and bank login — for as little as $20. According to the 2025 Dark Web Pricing Index, a complete “fullz” package containing everything a thief needs to impersonate you sells for $20 and up. A corporate email login goes for as little as $5.
Most people assume identity theft happens to someone else. It doesn’t. It happens to the person who hasn’t checked yet.
In 2024 alone, data theft on the dark web surged by 15.4%, generating more than 2 million alerts for compromised personal data, according to the CRIF Cyber Observatory. That’s not a rounding error. That’s a wave, and it’s still building.
This post is your field guide to the hidden infrastructure criminals use to steal identities — the tools, the marketplaces, the techniques — explained in plain language so you know exactly what you’re up against. More critically, you’ll find out how to check whether your own data is already out there, and what to do if it is.
By the end of this post, you will know exactly how to protect yourself, what warning signs to watch for, and which free tools you can use today to find out if hackers already have your information.
What the Dark Web Actually Is (And Why It Matters for Your Identity)
Most people picture the dark web as some neon-lit cyberpunk underworld. The reality is more mundane, and more dangerous for exactly that reason.
The dark web is a small, intentionally hidden section of the internet that standard browsers cannot access. To reach it, users need specialized software — most commonly the Tor browser, which routes traffic through multiple encrypted layers to hide the user’s identity and location. It’s like sending a letter through a dozen anonymous post offices before it reaches its destination.
Not everything on the dark web is illegal. Journalists, activists, and whistleblowers use it for privacy. But it has also become the preferred operating environment for organized cybercrime, and its anonymity makes enforcement extraordinarily difficult.
Here’s the scale of the problem in 2025. The dark web hosts an estimated 2 to 3 million daily users. Approximately 15 billion stolen credentials currently circulate across its markets and forums. Identity theft alone accounts for more than 65% of all monitored illegal activity on dark web platforms, according to research firm Sixgill.
Law enforcement runs regular operations — in May 2025, Operation RapTor seized $200 million and arrested 270 suspects. But as one marketplace goes down, another fills the gap within weeks. The underground economy is resilient by design.
What does this mean for you personally? It means that every major data breach you’ve ever heard of — and dozens you haven’t — has fed information directly into this ecosystem. Your email and password from that 2021 LinkedIn breach? Likely still circulating. Your credit card from a restaurant POS compromise three years ago? Probably already traded five times.
The dark web didn’t create identity theft. It industrialized it.
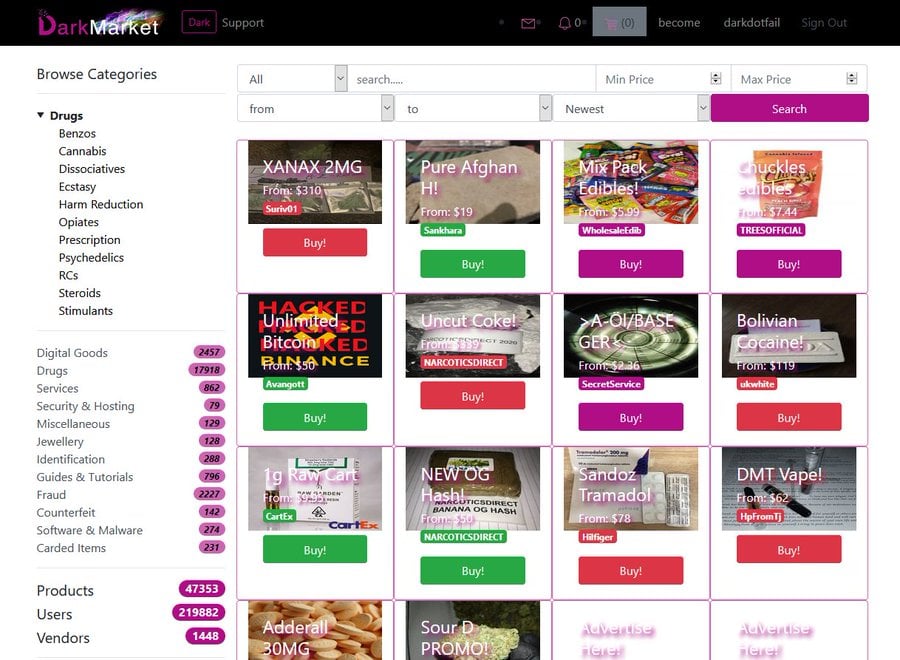
The Shocking Underground Marketplace Where Your Identity Gets Sold Like Groceries
Think of a dark web identity marketplace as Amazon, but for stolen personal data. It has product listings, customer reviews, pricing tiers, and even bulk discounts.
These markets operate on the Tor network and accept payment exclusively in cryptocurrency — primarily Bitcoin and Monero — to ensure transactions leave no traceable financial trail. The research firm LexisNexis Risk Solutions studied these markets extensively in 2025 and found that many come complete with tutorial videos showing first-time criminals how to use the stolen data. It’s a full-service criminal franchise.
Here’s what’s for sale, and what it costs:
- Email address + password combo: $1 to $5
- Full name, SSN, and date of birth: $20 and up
- Driver’s license scan: $20 to $200 depending on the issuing state
- Passport scan: $100 to $800
- Full “fullz” identity package (name, SSN, DOB, address, bank login, credit card): $300 to $1,500
- Corporate email login credentials: $5 to $500 depending on company size and access level
- Pre-verified “fraud-ready” bank accounts: $500 to $2,000
A single corporate email login could grant access to internal systems, client data, and financial accounts. A full fullz package gives a criminal everything they need to take out a loan, file a fraudulent tax return, or open new credit lines — all in your name.
The most chilling part? Most victims find out months or years after the sale. By then, the damage is done.
The Hidden Toolkit: 7 Dark Web Tools Hackers Use to Steal Identities
This is where it gets specific. Hackers don’t just browse the dark web for data. They use a layered toolkit of specialized software to find, steal, and monetize your personal information. Understanding these tools changes how you think about your own digital exposure.
1. Infostealer Malware: The Silent Pickpocket on Your Device
Infostealers are a category of malware designed to harvest credentials, cookies, autofill data, and payment information from your device — without you ever noticing. Programs like RedLine, Raccoon Stealer, and Vidar operate silently in the background after being installed through malicious downloads, fake software updates, or phishing links.
Once active, an infostealer sends your stored passwords, saved credit card details, and active browser sessions to the attacker’s server within minutes. IBM X-Force reported a 12% increase in infostealer listings on the dark web in 2024. These tools are sold as subscription services on dark forums, meaning even unskilled criminals can deploy them with minimal technical knowledge.
The takeaway: Never download software from unofficial sources. Keep your antivirus updated with real-time scanning enabled. Disable browser autofill for sensitive accounts and use a dedicated password manager instead.
2. Credential Stuffing Tools: Using Your Old Passwords Against You Right Now
Credential stuffing is devastatingly simple. Hackers take a list of usernames and passwords harvested from one breach and automatically test them against dozens of other websites. Tools like Sentry MBA, STORM, and SilverBullet automate this process at massive scale, testing thousands of credential pairs per minute.
The attack works because most people reuse passwords. A 2024 study found that the most common combination exposed on the dark web is still an email address paired with a reused password — present in 89.6% of dark web data exposures. If you use the same password for your email and your bank, one old breach can unlock everything.
Credential stuffing was the attack vector behind some of the most high-profile account takeovers of recent years, including attacks on streaming services, financial platforms, and healthcare portals. The attacker never needed to hack anything directly. They just used the keys you left lying around.
The takeaway: Use a unique, strong password for every account. A zero-knowledge password manager makes this practical without requiring you to memorize 80 different strings of characters.
3. Phishing Kits as a Service: Renting a Fake Bank Website for $10
Phishing has evolved far beyond clumsy emails with obvious spelling errors. Today’s dark web markets sell complete phishing kits — turnkey packages containing a convincing replica of a bank, government agency, or popular service, complete with hosting, templates, and automated data collection.
According to dark web monitoring data, phishing kits and hijacked domains are traded daily on underground forums. Some groups sell “phishing as a service,” where the criminal pays a subscription fee and the service provider handles everything, including sending emails, hosting the fake site, and forwarding stolen credentials in real time.
Illustrative scenario: A small business owner receives an email that looks exactly like their bank’s fraud alert system. They click through, enter their login credentials on what appears to be the bank’s website, and unknowingly hand their access directly to an attacker. The entire kit that enabled this attack cost the hacker $10.
The takeaway: Always verify website URLs before entering credentials. Bookmark your bank’s actual login page and never use links from emails, even ones that look legitimate.
4. WormGPT and FraudGPT: AI-Powered Phishing That’s Nearly Impossible to Spot
This is where the threat gets genuinely terrifying. Cybercriminals now have access to underground AI language models — tools like WormGPT and FraudGPT — that are sold directly on the dark web. These are uncensored variants of large language models, stripped of safety guardrails and purpose-built for malicious use.
These tools generate hyper-personalized phishing emails using scraped data from LinkedIn and social media. They can craft messages in dozens of languages, tailor the tone to match a specific company’s communication style, and pass through spam filters by mimicking natural human writing patterns.
According to cybersecurity reporting, these tools allow criminals to launch targeted attacks at scale that would previously have required a team of skilled social engineers. A single operator can now run thousands of convincing, personalized fraud campaigns simultaneously. The FBI’s Internet Crime Report for 2025 linked AI-powered cybercrimes to over $14 billion in reported losses, a figure up nearly 60% from the previous year.
The takeaway: No email is safe to act on reflexively. When something asks you to click, verify, or enter credentials, pause and verify the request through a separate, trusted channel — call the company directly.
5. Account Takeover (ATO) Services: Outsourcing Identity Theft to Professionals
Account takeover has become a service industry. Dark web markets now offer ATO-as-a-service, where a buyer pays a fee and receives access to an already-compromised account — email, social media, financial, or corporate. The groundwork has been done for them.
These services use a combination of the tools already described: infostealers to harvest credentials, credential stuffing tools to validate them, and then human operators or bots to defeat security questions and two-factor authentication through social engineering or SIM swapping.
Illustrative scenario: A fraudster purchases access to a compromised corporate email account from a dark web marketplace. Using that inbox, they send a wire transfer request to the finance department, impersonating an executive. This is called Business Email Compromise (BEC), and it costs businesses billions annually. The FBI has named it the costliest cybercrime category for years running.
The takeaway: Enable alerts on all financial accounts for any transaction or login from an unfamiliar device. Treat any unexpected wire transfer request as suspicious, even if it appears to come from a known internal address.
6. SIM Swapping Services: Hijacking Your Phone Number in Hours
SIM swapping is a technique where an attacker convinces your mobile carrier to transfer your phone number to a SIM card they control. Once they own your number, every SMS-based two-factor authentication code gets sent directly to them.
This attack is frighteningly accessible. Dark web forums host detailed guides, and in some cases, criminals with contacts at mobile carriers sell SIM swap services for a flat fee. A successful SIM swap gives the attacker the ability to reset passwords on your email, bank, and social media accounts, locking you out entirely within minutes.
High-profile targets have lost hundreds of thousands of dollars in cryptocurrency through SIM swapping. But this attack doesn’t only hit wealthy targets. Anyone using SMS-based 2FA is at some level of exposure.
The takeaway: Move away from SMS-based two-factor authentication wherever possible. Authenticator apps generate codes locally on your device and are not vulnerable to SIM swapping. For high-value accounts, a hardware security key provides the strongest available protection.
7. Data Broker Aggregation: Building a Dossier From Legal Sources
Not all of the data hackers use is stolen. A significant portion comes from entirely legal data brokers — companies that collect, compile, and sell personal information gathered from public records, loyalty programs, survey responses, and social media activity.
Hackers cross-reference information from data brokers with stolen data from breaches to build comprehensive profiles. Your name and employer from a data broker, combined with a leaked email and password from a breach, combined with your home address from a property record, creates a detailed dossier that enables highly targeted spear phishing, social engineering, and identity fraud.
This hybrid approach is increasingly common and particularly effective because the victim often can’t trace the attack to a specific breach. There was no single moment when their information was “stolen.” It was assembled, piece by piece, from multiple sources.
The takeaway: Regularly search your name on people-finder sites and submit opt-out requests. Several privacy-focused services automate this process continuously, as new data appears regularly.
Old Threats vs. New Reality: A Direct Comparison of How Identity Theft Has Evolved
Understanding how dramatically the threat has changed in just five years helps you calibrate your defenses accurately.
| Attack Method | Pre-2020 Approach | 2024–2025 Reality | Risk Level | Defense |
|---|---|---|---|---|
| Phishing emails | Generic, obvious spelling errors, mass sent | AI-generated, personalized, brand-perfect replicas | Critical | Verify via separate channel; never click email links |
| Credential theft | Manual brute force attacks | Automated credential stuffing with million-record breach lists | Critical | Unique passwords + password manager |
| Identity fraud | Required in-person forgery | Synthetic identities combining real + fake data with deepfakes | Severe | Credit freeze + dark web monitoring |
| SIM swapping | Required carrier insider access | Dark web services for hire, available to any buyer | High | Authenticator apps + hardware security keys |
| Data harvesting | Targeted corporate espionage | Automated infostealers deployed via phishing links | High | Real-time antivirus + endpoint protection solution |
| Marketplace access | Required significant technical skill | Turnkey dark web marketplaces with tutorial videos for beginners | Extreme | Proactive dark web monitoring + identity threat detection |
The pattern is clear. Every attack that once required skill, time, and resources has been democratized. The dark web didn’t just lower the barrier to entry for cybercrime — it eliminated it for anyone willing to pay.
According to the Verizon Data Breach Investigations Report, stolen credentials remain the single most common entry point for data breaches, year after year. The attack methods evolve. The underlying vulnerability — your credentials circulating somewhere you can’t see — stays constant.
The Biggest Misconception About Identity Theft: “I Don’t Have Anything Worth Stealing”
This belief is the single most dangerous thing a person can think about their own security. It is also completely wrong, and understanding why changes everything.
Cybercriminals don’t evaluate targets the way a burglar evaluates a house. They don’t scan for wealthy individuals or high-profile accounts. They run automated systems against massive credential lists. Your email and password appear in a breach. A tool tests it against 50 websites. Three of them work. The attacker sells the access, collects a few dollars, and moves on. The whole process took seconds and required no human judgment at all.
Your personal information has value independent of your income or status. Your Social Security number enables tax fraud, not luxury purchases. Your email access enables business email compromise scams targeting your employer. Your medical insurance number enables healthcare fraud. Your identity, combined with a small loan taken out in your name, enables credit fraud that takes years to untangle.
Synthetic identity fraud is the fastest growing category in this space. Criminals blend your real Social Security number with a fabricated name and address to create a new, “synthetic” identity that doesn’t match any real person — making it invisible to standard fraud detection systems for months or years.
The 2025 cybersecurity predictions from NordVPN’s research team highlighted synthetic identity fraud as a primary emerging threat, noting that deepfake technologies are now being integrated into these schemes to defeat biometric identity verification. This is not a future threat. It is happening now.
If you have a Social Security number, a bank account, or a job, you have something worth stealing.
How Hackers Know Exactly What to Use Against You: The Art of Profiling Victims
Once a hacker has your email and a few data points, the profiling begins. This section reveals the hidden process that transforms a leaked credential into a targeted attack.
Step one is cross-referencing. Your leaked email gets checked against multiple breach databases to identify every platform you’ve registered with. Step two is enrichment — your email domain, name, and employer get pulled from LinkedIn and data brokers. Step three is priority scoring — accounts with access to financial systems, cloud storage, or corporate networks get flagged for higher-value exploitation.
The combination of your home address (from a data broker) with your phone number (from a breach) with your employer (from LinkedIn) creates the raw material for vishing — voice phishing calls where the criminal already knows enough about you to sound credible and authoritative.
A real-world pattern documented by security researchers: An attacker calls a target claiming to be from their bank’s fraud department. They know the target’s name, last four of their card, recent transaction amounts, and home address — all assembled from publicly available sources and dark web purchases. The target, convinced the caller is legitimate, provides the remaining information needed to complete an account takeover.
This is social engineering at its most effective, and it works because the attacker starts the conversation knowing more about you than you expect a stranger to know.
The takeaway: Treat any inbound call requesting verification as suspicious, regardless of how much they already seem to know. Hang up and call the institution directly using the number on their official website.
Your 7-Step Action Plan to Protect Your Identity From Dark Web Threats
You now know what hackers use and how they work. Here’s what to do about it, in order of impact.
1. Run a free dark web scan today. Start with HaveIBeenPwned (haveibeenpwned.com) — a trusted, free tool that checks your email address against a database of nearly 15 billion breached records across hundreds of breached platforms. Take five minutes to do this right now, before you read the next step. If your email appears in breaches, you need to know which accounts were affected and act immediately.
2. Enable dark web monitoring on an ongoing basis. A one-time scan is a snapshot. Your data can appear on the dark web weeks or months after a breach, when the data is sold for the first time. Services like Google’s Dark Web Report (available in the Google app), Mozilla Monitor, and premium identity protection platforms offer continuous monitoring and alert you when new exposure is detected. Ongoing monitoring is the difference between catching a problem in days and discovering it in years.
3. Freeze your credit at all three major bureaus. A credit freeze is free, reversible, and prevents any new credit accounts from being opened in your name — even if a thief has your SSN. You need to freeze separately at Equifax, Experian, and TransUnion. This single step eliminates the most financially damaging category of identity fraud. If you suspect your SSN has been compromised, do this today, not next week.
4. Replace SMS-based 2FA with an authenticator app. Log into every important account — email, bank, social media, cloud storage — and switch from SMS verification codes to an authenticator app that generates time-based codes locally on your device. This eliminates SIM swapping as an attack vector. For your most critical accounts, upgrade further to a hardware security key, which provides phishing-resistant MFA that cannot be stolen remotely under any current attack method.
5. Audit your password hygiene with a zero-knowledge password manager. A zero-knowledge password manager stores your credentials in an encrypted vault that only you can unlock. Use it to generate a unique, randomly generated password for every account you own. If one account is breached, no other account is affected. The manager handles memorization; you handle one strong master password. This one change neutralizes credential stuffing attacks entirely.
6. Opt out of data brokers systematically. Search your name on major people-finder and data broker sites. Most offer opt-out forms, though the process is time-consuming if done manually. Privacy-focused services automate this process, scanning for and submitting removal requests across hundreds of data broker sites continuously. Reducing your surface area on the open web limits the profiling data available to criminals for targeted attacks.
7. Set up financial and account alerts across every platform. Every bank, credit card issuer, and investment account offers transaction alerts. Enable them for all transactions, not just large ones. Also enable login alerts on your email and social media accounts. Early warning of unauthorized activity dramatically limits the damage, and in many cases, alerts will notify you of an attack before the attacker has had time to act on the access they’ve gained.
None of these steps require technical expertise. All of them are free or low-cost. The only thing they require is fifteen minutes and the decision to treat your identity the same way you treat your physical wallet.
Warning Signs You May Already Be a Victim of Dark Web Identity Theft
Sometimes you don’t need a dark web scan to know something is wrong. These are the signals most people miss.
Watch for these red flags:
- Unexpected credit inquiries on your credit report — these indicate someone has applied for credit in your name
- Bills or collection notices for accounts you never opened
- Tax return rejection by the IRS, indicating a return has already been filed with your SSN
- Medical bills for services you never received, or insurance claims denied because benefits have been exhausted
- Login notifications from accounts you haven’t accessed recently
- Calls from debt collectors about debts you don’t recognize
- Accounts locked or passwords changed without your initiation
Any one of these signals warrants immediate action: check your credit report at annualcreditreport.com, file a report at IdentityTheft.gov, and contact your financial institutions directly.
Real-World Case Study: How a Small Business Owner Became a Victim Without Clicking a Single Phishing Link
This is an illustrative composite scenario based on documented attack patterns, provided to show how multiple dark web tools work in combination.
Who: A small business owner running a 12-person marketing agency.
What happened: A data broker had compiled a profile including her name, home address, employer, and phone number from public records and social media. Separately, her email and password from a 2019 service breach were circulating on a dark web forum.
A credential stuffing tool tested the breach credentials against her business bank’s portal. Her password matched. The attacker now had read access to the business account.
Before taking action, the attacker ran her phone number through a SIM swap service purchased for $150 on a dark web marketplace. Within four hours, her mobile number transferred to a new SIM card the attacker controlled.
Using her phone number, the attacker reset her email password. Using her email, they reset her banking password. Using her banking access, they initiated two outbound wire transfers totaling $34,000 to overseas accounts over 48 hours.
The mistake: She had used the same password from 2019 on her current business banking portal and was using SMS-based two-factor authentication.
The cost: $34,000 in direct financial loss. Three weeks of operational disruption. Six months of legal and remediation processes.
The lesson: The attack used no zero-day vulnerabilities, no sophisticated hacking, and no phishing emails. It used old, recycled data from a breach she had forgotten about, combined with a for-hire service purchased for $150. The entire infrastructure was assembled from tools available on any dark web marketplace.
An identity threat detection platform and a password audit would have identified the reused credential before the attack ever began.
Expert Insight: What Security Researchers Say Is Coming Next
The threat landscape in 2025 and 2026 is being shaped by two converging forces: the increasing sophistication of AI-generated fraud and the emergence of synthetic identity theft at scale.
Security researchers at NordVPN’s threat intelligence division highlighted synthetic identity fraud as a top emerging concern, noting that criminals now blend real Social Security numbers with fabricated biographical data to create identities that bypass standard verification systems. These synthetic identities accumulate credit history over months before the fraud is activated, making detection extremely difficult.
A nuanced point worth acknowledging: not every piece of dark web data results in immediate harm. Much of the stolen data circulating in underground markets is old, outdated, or incomplete. However — and this is the critical caveat — criminals are increasingly using AI-powered enrichment tools to cross-reference and fill in gaps across multiple data sources. Old data combined with new public information creates a complete profile. The age of the breach doesn’t protect you.
According to the World Economic Forum’s Global Risks Report, cyberattacks ranked as the fifth most severe global risk over the next two years, with AI-generated fraud and disinformation compounding the challenge for individuals and institutions alike.
The direction of travel is clear: attacks are becoming cheaper, faster, and harder to detect. Defenses that worked in 2022 are inadequate for the threat environment of 2025.
The Tools Built to Fight Back: How to Monitor the Dark Web for Your Own Data
You cannot access the dark web safely without specialist knowledge, and you shouldn’t try. But you can use legitimate monitoring tools that do the crawling for you and alert you when your information surfaces.
Here’s a clear breakdown of your options:
| Tool | Cost | What It Monitors | Best For | Key Limitation |
|---|---|---|---|---|
| HaveIBeenPwned | Free | Email, phone number | Quick initial breach check | Point-in-time, not continuous |
| Google Dark Web Report | Free (Google account) | Email, phone, name | Ongoing basic monitoring | Limited to saved profile data |
| Mozilla Monitor | Free / Paid | Email + data broker removal | Privacy + breach monitoring combined | Premium needed for full coverage |
| Experian Dark Web Scan | Free (one-time) | SSN, email, phone | SSN-specific exposure check | One-time only without subscription |
| Aura / Identity Guard | Paid | SSN, financial accounts, credit, identity | Comprehensive ongoing protection | Subscription cost |
| Keeper BreachWatch | Paid add-on | Stored passwords and credentials | Password-specific monitoring | Requires Keeper password manager |
The right tool depends on your risk profile. If you’ve never checked, start with HaveIBeenPwned today. If you’ve had a data breach notification, or if you work in a role with financial or administrative access, a paid monitoring service with SSN tracking is worth the investment.
FAQ: Your Most Pressing Questions About Dark Web Identity Theft, Answered
Can hackers really steal my identity using just my email address?
An email address alone isn’t enough to steal your identity, but it’s a critical starting point. Combined with a leaked password from a data breach, your email grants access to any account where you’ve reused that password. From your email inbox, an attacker can reset passwords on your bank, social media, and other accounts. They can also use your email to receive SMS codes if they’ve already carried out a SIM swap. The email address is the master key, and the password is the lock — if that lock has appeared in any breach, you’re exposed.
How do I know if my personal information is already on the dark web?
The fastest way is to run a free scan using HaveIBeenPwned, which checks your email against nearly 15 billion breached records. For more sensitive data — your Social Security number, financial details, or physical ID documents — you need a dedicated dark web monitoring service, since free tools only check email and passwords. Google’s Dark Web Report is a free option for broader monitoring if you have a Google account. Paid services offer continuous, comprehensive monitoring and immediate alerts.
What should I do immediately if I find my information on the dark web?
First, change the passwords on every account associated with the exposed email — prioritizing financial, email, and any account with stored payment information. Second, enable an authenticator app for two-factor authentication on those accounts. Third, check your credit report at annualcreditreport.com for unauthorized accounts or inquiries. Fourth, freeze your credit at all three bureaus if your SSN was part of the exposure. Fifth, file a report at IdentityTheft.gov if you find evidence of fraud. Speed matters — the faster you act, the less damage occurs.
Does dark web identity theft only happen to people who use risky websites?
No. Most people whose data ends up on the dark web never did anything wrong. Their information was exposed in a breach at a company they trusted — a retailer, healthcare provider, employer, or government agency. You have no control over how companies store and protect your data. This is why dark web monitoring is essential: it’s not a reward for safe behavior. It’s a defense against other people’s security failures that affect you.
Are dark web monitoring services actually worth paying for?
For most people, yes — particularly if your SSN, financial accounts, or professional credentials are involved. Free tools only check email and passwords. Paid monitoring services track your Social Security number, financial account details, physical ID documents, and credit activity in real time. They also typically include identity restoration support and insurance coverage for losses if theft occurs. The cost is usually less than $15 per month — a fraction of the average financial loss from identity theft, which runs into the thousands.
Conclusion: The Clock Is Running, Whether You’re Watching It or Not
Return to where this post started. Your personal data may be listed for sale on a dark web marketplace right now. The sale price is lower than your morning coffee. The buyer could be anyone.
Here are the three most critical insights to carry with you. First, the dark web identity theft industry is professionalized and scalable. Hackers don’t need to target you specifically. Automated systems do the work, and your data is simply one entry in a list of millions. Second, the tools they use — infostealers, credential stuffers, AI phishing generators, SIM swap services — are all accessible, cheap, and continuously evolving. Third, you can fight back effectively, but only if you act proactively. Reactive defense after identity theft is costly, slow, and emotionally exhausting.
The dangerous temptation is to read this post, feel the urgency, and then get pulled back into the day by something less unpleasant. That window of inaction is exactly what criminals rely on.
Every day you wait to run a dark web scan is a day you don’t know what you’re dealing with. Every day you reuse a password is a day a single old breach can unlock your financial life. Every day you rely on SMS two-factor authentication is a day a $150 SIM swap service can hand your accounts to a stranger.
The most important thing you can do right now — not tomorrow, right now — is go to haveibeenpwned.com, enter your email address, and find out where you stand. What you find might change everything.
Your identity is the one asset you cannot replace. Defend it like it.